- Can't be uninstalled via Control Panel
- Block exe files from running
- Installs itself without permissions
- Connects to the internet without permission
- System crashes
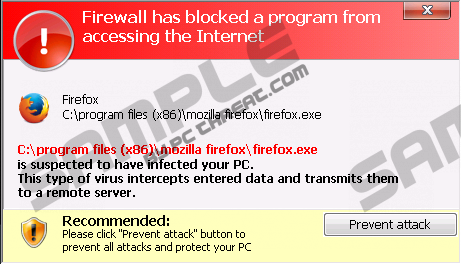
- Annoying Pop-up's
- Slow Computer
Windows Defence UnitAre you seeing various warnings that your system is infected with malicious software? If it is exactly so, it is very probable that your computer is infected with a rogue application better known as Windows Defence Unit. It is an application that belongs to FakeVimes family of infections; thus, you should not expect anything beneficial from it. It is known that this program seeks to scare computer users and thus easily extort money from them. Actually, you should not trust any word of Windows Defence Unit because it is simulated security software. It might appear on all the computers with Windows operating system, which is why we recommend that you keep your antimalware tool enabled. Do you already have Windows Defence Unit on your system? You should better get rid of it as soon as possible. As the main purpose of this application is to make you believe that your computer is infected, it is not surprising that Windows Defence Unit is going to perform a scan and then provide you with a list of malicious software that has supposedly entered your system. Do not be scared; these threats do not exist onto your computer; however, it is still possible that you have other infections like Trojan on your PC. As you might have already understood, you should not believe any promises of Windows Defence Unit because it is not going to do anything good for you. What is more, you should not buy the license that costs $99.9 because you will not only lose your money, but also reveal your credit card details. It means that the possibility that all your money will be stolen is rather high. Thus, if you have already paid money, we recommend that you call your credit card issuer and ask to cancel the payment. However, your credit card information might be already known for cyber criminals; thus, you should be very careful. The removal of Windows Defence Unit is not very easy because it does not allow accessing Task Manager, Registry Editor, Internet and other essential tools. Thus, you should enter 0W000-000B0-00T00-E0022 or 0W000-000B0-00T00-E0021 and all the annoying symptoms will be gone. Then, you will have an opportunity to erase the program itself. For this matter, SpyHunter antimalware suite is the most suitable. Windows Defence Unit removal
| ||||||||||
|
Download Spyware Removal Tool to Remove*
Windows Defence Unit
| ||||||||||

|
How to manually remove Windows Defence Unit
Files associated with Windows Defence Unit infection:
%AppData%\svc-[random file name].exe
Windows Defence Unit processes to kill:
Remove Windows Defence Unit registry entries:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\k9filter.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpCmdRun.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpUXSrv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msmpeng.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msseces.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\bckd
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\bckd "ImagePath" = "123123.sys"

Post comment — WE NEED YOUR OPINION!