- Blocks internet connection
- Block exe files from running
- Installs itself without permissions
- Connects to the internet without permission
- Normal system programs crash immediatelly
- Slow internet connection
- System crashes
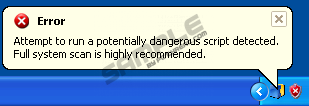
- Annoying Pop-up's
- Slow Computer
Windows Software SaverHave you noticed that your computer is under an attack of a sinister computer infection Windows Software Saver? Then there is no time to waste, as this malicious application will get into your head and make you believe that you need to purchase Windows Software Saver’s full version, which supposedly is the only way to remove any Trojans and viruses attacking your PC. Do not believe that any of this is true, because neither the tool nor the multiple infections are real and legitimate! If you spend your money onto useless Windows Software Saver tools, you will only throw your money onto something you do not need, and will expose your personal details (credit card number, full name, address, etc.) to cyber criminals, who will be able to link you and your identifying information to other schemes. Cyber criminals, who have generated Windows Software Saver, know very well that different PC users have different browsing and downloading habits, this is why various security cracks and loopholes have been implemented to involve the maximum number of people. You could catch Windows Software Saver’s infection via bundled downloads, Trojans, disguised software (e.g. fake video codecs), online scanner of various other deceitful backdoors, so be careful when you wander around the virtual space, and follow any sort of directions. Windows Software Saver is a double-faced application, which will mimic the infection and, at the same time, will cause serious Windows dysfunctions. You will be forced to believe the threats, because once Windows Software Saver infiltrates, you might loose access to important Windows tools. In reality, Windows Software Saver’s hackers simply create these distressing malfunctions, to hide malicious processes from being removed! To strengthen the infection’s credibility, you will also be flooded with fake security alerts. It is essential to introduce your PC to veritable antispyware and antivirus tools, because only they will be able to detect and remove Windows Software Saver with all of its components. If you are thinking about manual removal option, evaluate your Windows knowledge thoroughly, and only if you have removed malware before, should you go ahead with this task. UPDATETo add, there is nothing good about Windows Software Saver that might actually save your system. It can only damage it and prevent you from using your favorite programs. This is one of Windows Software Saver's abilities - blocking your executables. The rogue shares this feature with the other infections from the Rogue.VirusDoctor family including Windows Sofware Keeper, Windows Safety Tweaker, Windows AntiHazard Helper and the like. On top of that, Windows Software Saver can also block your Task Manager, Registry Editor and Internet connection. The rogue says it does so in order to protect your system from further infections, but Windows Software Saver just wants to make sure that you will not be able to remove it. Thus, it puts you in a tight corner when there is no other way to get out, but to pay for the full version of Windows Software Saver, right? Wrong! Keep your credit card information to yourself, and do not even consider this option. In order to erase Windows Software Saver first and foremost you must ignore the fake security messages that the rogue sends you: Error Warning! Identity theft attempt Detected Warning The messages are generated to cause you to panic, but there is nothing real about them. Next, you should tame Windows Software Saver by clicking the blue "Activate Ultimate Protection" button and entering the following code: 0W000-000B0-00T00-E0020 The rogue will take this as a sign that you have purchased the license and will calm down. Then you will be able to remove Windows Software Saver at ease, using a reliable antimalware tool, if you cannot terminate a rogue on your own.
Download Spyware Removal Tool to Remove* Windows Software Saver
How to renew your internet connection:This rogue antispyware blocks your Internet connection to prevent you from removing the rogue application. To enable the Internet connection, please follow these instructions:
| ||||||||
|
Download Spyware Removal Tool to Remove*
Windows Software Saver
| ||||||||

|
How to manually remove Windows Software Saver
Files associated with Windows Software Saver infection:
%CommonStartMenu%\Programs\Windows Software Saver.lnk
%AppData%\result.db
%AppData%\Protector-[Random].exe
%AppData%\NPSWF32.dll
Windows Software Saver DLL's to remove:
Windows Software Saver processes to kill:
Remove Windows Software Saver registry entries:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Settings "UID" = "okanrqfdwk"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\atro55en.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\bisp.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\esafe.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\install[4].exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mssmmc32.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\pcip10117_0.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\scrscan.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\utpost.exe






Post comment — WE NEED YOUR OPINION!